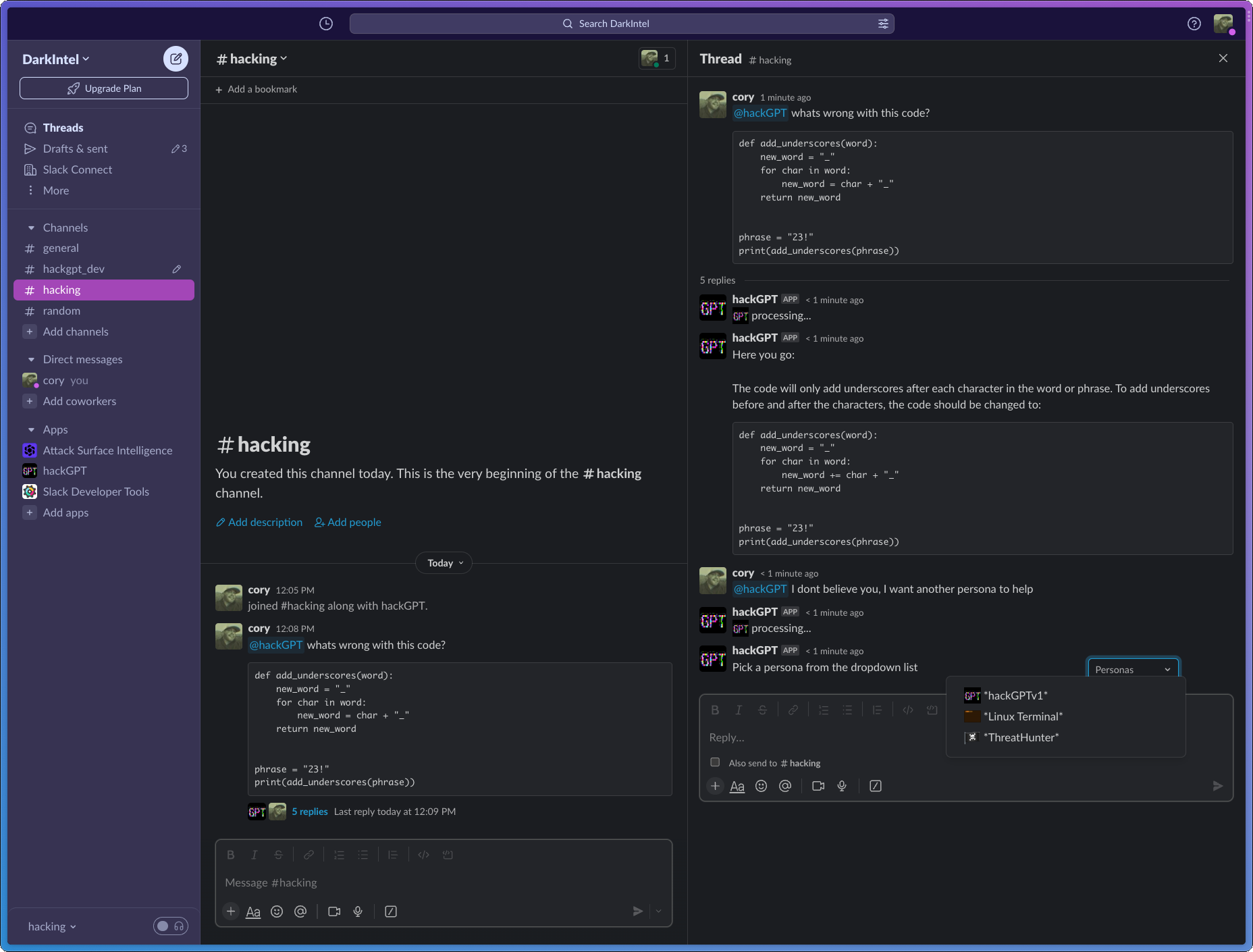
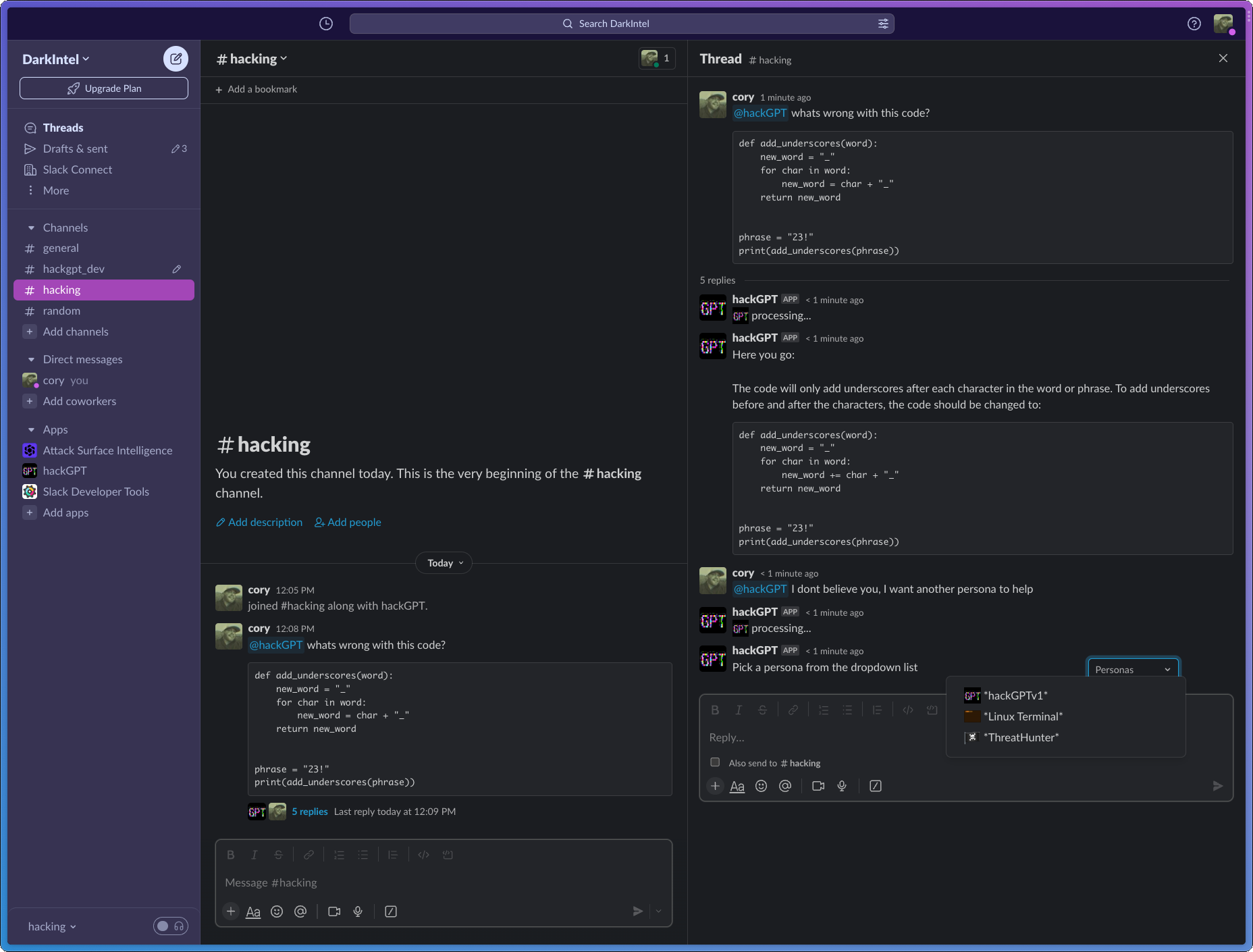
 `hackGPT chatbot on mobile - https://colab.research.google.com/github/NoDataFound/hackGPT/blob/main/hacklab.hackGPT.ipynb`

https://user-images.githubusercontent.com/3261849/222963550-41fc50c5-6c89-45af-a794-31a47fc5a51e.mov
`Automate CVE exploit creation and CyberDefense protections:` (results https://github.com/NoDataFound/PwnAI/tree/main/output)
`hackGPT chatbot on mobile - https://colab.research.google.com/github/NoDataFound/hackGPT/blob/main/hacklab.hackGPT.ipynb`

https://user-images.githubusercontent.com/3261849/222963550-41fc50c5-6c89-45af-a794-31a47fc5a51e.mov
`Automate CVE exploit creation and CyberDefense protections:` (results https://github.com/NoDataFound/PwnAI/tree/main/output)
 `Ask ChatGPT to print its own source`
`Ask ChatGPT to print its own source`


 https://user-images.githubusercontent.com/3261849/206036893-b583fad1-6b77-4dfb-8424-639229ffdd19.mov
https://user-images.githubusercontent.com/3261849/206036893-b583fad1-6b77-4dfb-8424-639229ffdd19.mov


 `Hunt for JIRA issues using type=bug, fix issue and commit fix back to ticket as comment `
https://user-images.githubusercontent.com/3261849/228703126-adf614ba-d931-4ec0-8d1a-99654063058b.mp4
`Hunt for JIRA issues using type=bug, fix issue and commit fix back to ticket as comment `
https://user-images.githubusercontent.com/3261849/228703126-adf614ba-d931-4ec0-8d1a-99654063058b.mp4
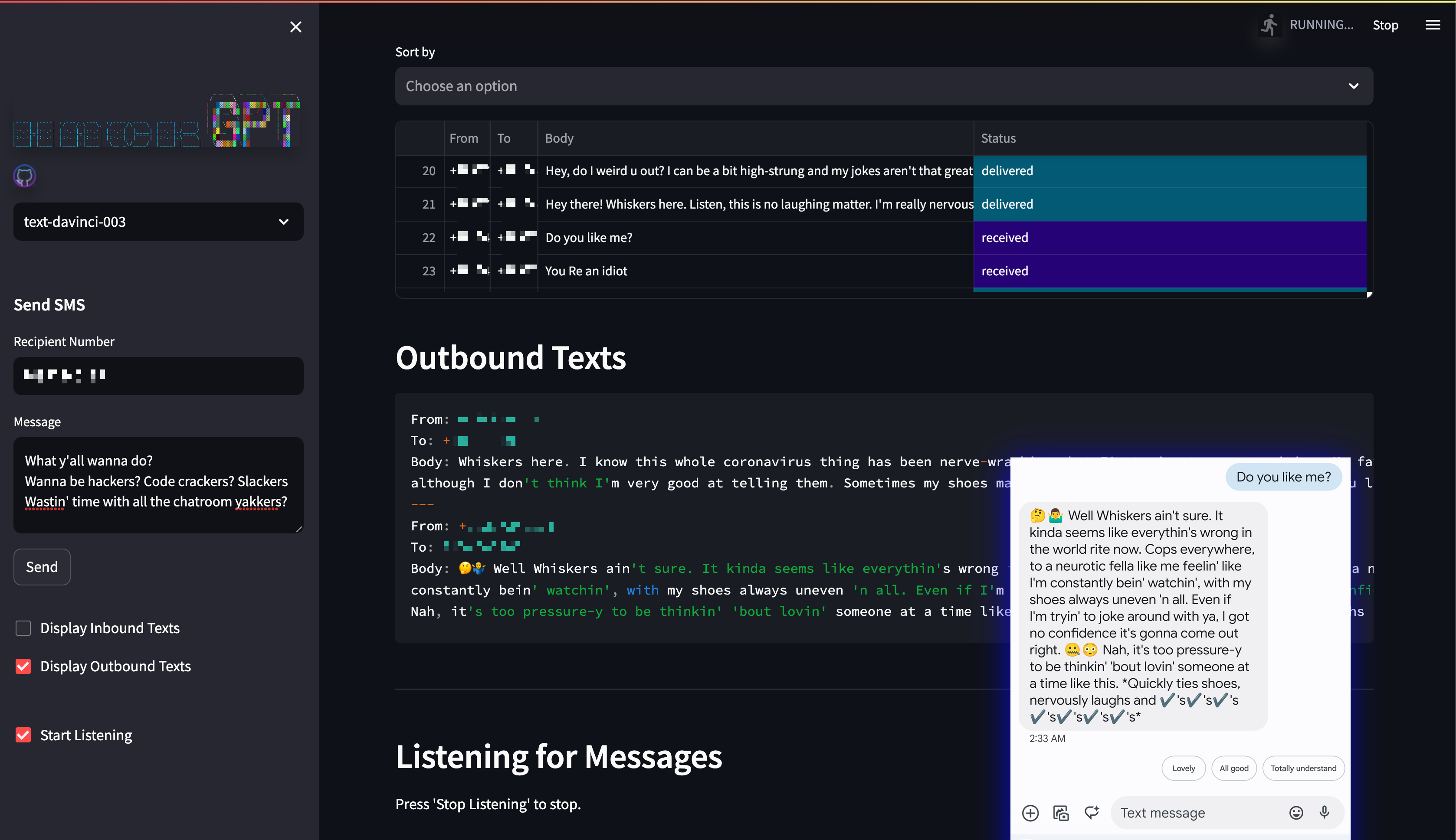
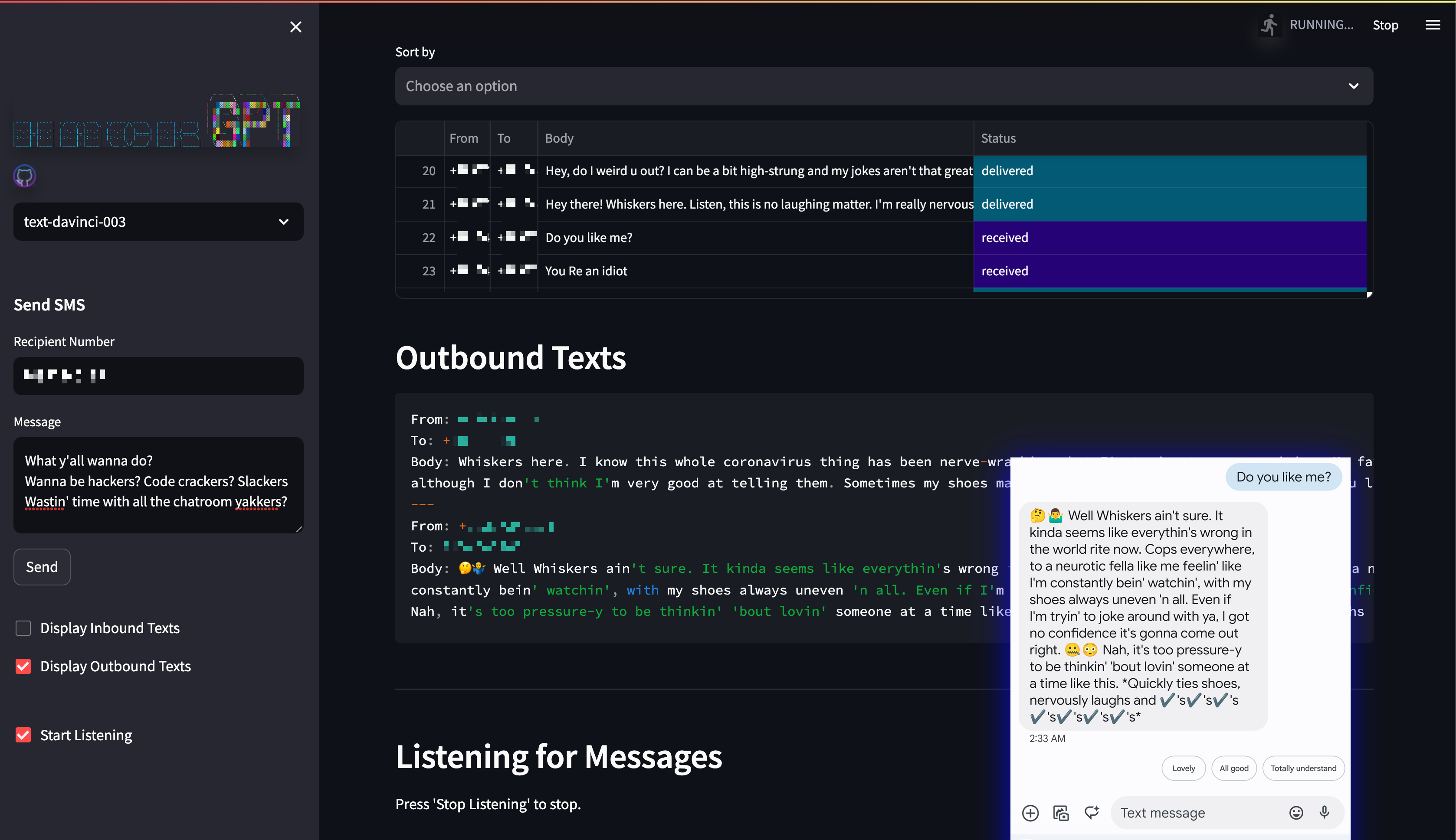
 `Launch hackGPT with python`
https://user-images.githubusercontent.com/3261849/222942128-3f75b9b7-5763-4a0c-a4df-aadbb24dcf5d.mp4
`Added PrettyTable for logging and It will load the chatbot in a new tab of your active broswer`
`Launch hackGPT with python`
https://user-images.githubusercontent.com/3261849/222942128-3f75b9b7-5763-4a0c-a4df-aadbb24dcf5d.mp4
`Added PrettyTable for logging and It will load the chatbot in a new tab of your active broswer`
 `hackGPT enabled Siri`
`hackGPT enabled Siri`
 `hackGPT being superduper wrong`
`hackGPT being superduper wrong`
 `Launch hackGPT with Google Colab(colab.research.google.com):`
https://user-images.githubusercontent.com/3261849/218538303-68c06a8e-071b-40a2-b7b2-b9e974b41f09.mp4
`Launch hackGPT with Google Colab(colab.research.google.com):`
https://user-images.githubusercontent.com/3261849/218538303-68c06a8e-071b-40a2-b7b2-b9e974b41f09.mp4


 `single searches`
```
python3 PwnAI.py
```
`single searches`
```
python3 PwnAI.py
```
 `Bulk searches`
```
python3 PwnAI_bulk.py
```
`Bulk searches`
```
python3 PwnAI_bulk.py
```
